
By Daniel Woods
The insurance industry is far from a “usual suspect” when it comes to offensive cyber operations. Insurers are neither belligerents, targets nor suppliers of offensive cyber capabilities. Yet they often find themselves footing the bill for the resulting damages. For example, the NotPetya attack—attributed to the Russian military—was estimated to have caused $3 billion of insured losses. Typically, insurers exclude coverage for losses caused by war. This raises the question of how insurers have excluded losses caused by offensive cyber operations?
The insurance industry have erred on the side of slow deliberation, especially with respect to cyber insurance products. This is not because the insurance practitioners are inherently more restrained, but instead because the structure of the industry rewards conformity.
The same restraint adds to the importance of two recent developments. First, in November 2021 an industry working group published contractual language drafted to apply to offensive cyber operations. Second, a court ruled in January this year that traditional war exclusions do not apply to the NotPetya cyber attack, notably this case concerned an all risks policy, not a standalone cyber product
Going forward, the insurance industry’s approach to offensive cyber may further shape discourses around offensive cyber by contesting the language of war clauses in a court of law and by adding information to the public record via the legal process of discovery. History has shown that exclusions can even undermine economic activities as businesses withdraw due to a lack of coverage.
War Exclusions in Cyber Insurance Policies
War clauses are included in insurance policies in order to invalidate coverage if the loss was caused by war and other external conflicts related events (e.g. warlike actions, hostilities and acts of foreign enemies). Typically, these clauses also exclude events caused by internal conflict (e.g. civil war, coup, and revolution). In some cases, events related to civil unrest (e.g. riot, strike or labor action, and lockout) are also part of a war clause. This raises the question of whether war clauses are included in cyber insurance policies, and how they are worded.
An in depth analysis of cyber insurance policies from 2008–2018 show that since 2012, all specialized cyber insurance policies include a war clause. In the first half of our sample, these war clauses were typically imported word-for-word from non-cyber insurance policies. This means they were drafted without offensive cyber operations in mind as they do not include language including the prefix cyber, electronic operations or similar. This began to change from 2015 onward.
The majority of the resulting cyber-specific clauses introduce the term “cyber terrorism”. This was not because actuaries had somehow quantified a shift in the risk landscape in which cyber terrorists played a greater role. Instead, the US Treasury clarified that the Terrorism Risk and Reinsurance Act (TRIA) applied to cyber insurance. This obligated insurance policies sold in the US to affirmatively state whether the policy covered acts of (now cyber) terrorism. This was typically done by including a “carve back” stating that the policy covers cases of cyber terrorism, but not any other losses that trigger the war clause. This potentially left courts with the task of adjudicating two questions, namely was the cause of the insured loss an act of traditional war, and was it an act of cyber terrorism? Coverage would only be invalidated if the answer was “yes, no”.
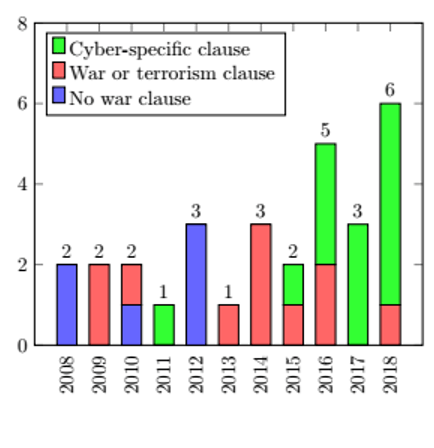
To summarize, the analysis illustrates how cyber insurance policies were not updated to reflect a growing narrative around cyber war and potential offensive cyber operations until at least 2018. In fact, the main driver of change was the US Treasury’s regulatory guidance. While some changes are beginning to filter through the industry, it is worth asking why insurers are so conservative when it comes to contractual language.
A Slow-Moving Industry
War clauses are not the only examples in which the industry has been slow to change. A general study of cyber insurance policies (looking at the whole contract and not just war clauses as in ours) did not reveal “any substantial changes in policy length, style, or composition over time” in a sample from 2007 to 2017. Even beyond contracts, an industry survey asked about the impact of ”systemic events such as the Dyn DDoS or the WannaCry Ransomware event” on cyber insurance assessment and pricing revealed that just 15% of insurance practitioners reported a moderate or significant change, with 45% reporting that there was no impact whatsoever.
It is worth sketching how change happens within the industry, or more importantly what structural factors inhibit change. Selling cyber insurance to large companies requires an unusual form of risk sharing between peer firms known as tower insurance. One firm offers coverage for the first $10 million of losses, another firm covers the next $15 million, a third the next $25 million, and so on. If a loss exceeds $50 million, then all three insurers pay out. Tower insurance is virtually the only way large corporations can secure cyber insurance with a limit of $100 million or more.
Typically, all layers of coverage are written with the same policy terms. In practice this means an individual insurer cannot experiment with novel cyber war exclusions without all the other insurers in the tower being on board. An additional force is that brokers would read the cyber war exclusion and immediately set about finding another insurer without the novel clause. Together these two effects, insurance towers and brokers, strengthen market norms about how cyber insurance policies should be written. This helps explain why the market was so slow to define cyber war and argue it in a court of law. Notably this changed in recent years, which we now consider.
Recent Developments
With enough time, even a slow-moving industry will get somewhere. Two processes culminated in the last year—the first was an industry push to craft a cyber-specific war clause, and the second was a court case asking whether the NotPetya attack could trigger a traditional war clause in an all-risks (not cyber) insurance policy.
First, the industry has been thinking about the problem of applying war exclusions to cyber incidents since at least 2016. In November 2021, an industry working group published the LMA Cyber War and Cyber Operation Exclusion Clauses, which exclude any claim due to a “cyber operation”. Interestingly, the primary factor in distinguishing a cyber operation from a generic cyber attack is whether the attack was attributed to “another state or those acting on its behalf” by the government in the location of the affected system. This is very similar to how insurance policies respond differently to “terrorism” but rely on governments to make the distinction. The Terrorism Risk Insurance Act (TRIA) in the US requires the US Treasury to cerify whether an event was an act of terrorism, with a similar mechanism for the Government’s Pool Re scheme in the UK. The interpretation of the new concepts and definitions will no doubt generate scholarship and court cases.
But we need not wait for the decision to see whether traditional war exclusions might be triggered by a cyber incident. In January 2022, a New Jersey court ruled in a dispute over $1.4 billion in losses that the war exclusion in Merck’s all-risks (not cyber) policy was not triggered by the 2017 NotPetya attack. The decision noted that “no court has applied a war (or hostile acts) exclusion to anything remotely close to the facts”. Further, the responsibility was on the insurer to communicate that offensive cyber operations would not be covered. This further motivates the relevance of the new LMA exclusions.
The Future of Insurance and Offensive Cyber Operations
Beyond analyzing the corpus of cyber insurance policies, our article identifies five ways in which the insurance industry impacts discourses on war.
1. Financial (F1) – Unavailability of risk transfer prompts risk withdrawal
Although obvious, insurance indemnifying the costs of offensive cyber operations makes the status quo more tolerable for private firms. In doing so, Virginia Haufler argues insurers are enabling commerce and prosperity. Withdrawing such coverage can halt economic activity. For example, the introduction of terrorism exclusions in property policies halted construction projects in the wake of 9/11. This raises the question of whether the aforementioned war clauses (or similar) could lead to a shift in either the economic activity or political demands of private firms.
2. Discursive (F2) – Contractual language and disputes produce argumentation
Insurers introduce language in policy contracts to exclude offensive cyber operations. The meaning of such definitions can be clarified in court disputes over whether an exclusion applies. This shifts the discourse towards legalistic reasoning. For example, arguments presented will be probed and critiqued by opposing lawyers and the quality of evidence will be assessed according to established standards. Neither process is available when security vendors attribute offensive cyber operations in white papers without peer review—as we saw earlier the LMA exclusions turn on this exact issue.
3. Informational (F3) – Evidence is produced and made public
Beyond the mode of reasoning, legal disputes may lead new documents to enter the public domain. The most striking example of this occurred during Pan Am v. Aetna 1973, an insurance dispute that hinged on whether a plane hijacking could trigger a war clause. The legal process of discovery was used to successfully to call government agencies (e.g. the State Department) to give evidence on the history of the Israeli–Palestinian conflict. Notably, the CIA refused to do so. In disputes over exclusions related to cyber incidents, novel documents could be unearthed by the discovery process.
4. Symbolic (F4) – Decisions inherit status and power from the legal system
A ruling in either direction confers the symbolism associated with the associated court. In Montoya v. United States, the Supreme Court ruled that property damage caused by indigenous tribes “acting in hostility to the United States” triggered a war clause. We saw this when the New Jersey Superior Court Judge Thomas Walsh rule that the NotPetya attack did not trigger the war clause found in Merck’s all-risks policy.
5. Active (F5) – Insurers actively shape security risks
Finally, insurers can re-structure the “strategic security environment”. This can be done either by publishing information like the Lloyd’s List, by requiring policies holders to implement security measures, or by influencing the political process. Ross Anderson predicted that insurers could lobby against offensive cyber operations way back in 1994. Notably, it is technology companies and not insurers who have set about doing so in recent years.
Conclusion
Offensive cyber operations have the potential to impact the insurance industry’s bottom line by causing many firms to make simultaneous claims. This was seen in the NotPetya attack in which the industry paid out billions of dollars to policyholders. Typically, insurers have controlled this existential risk via “war exclusions”. However, the New Jersey court ruling shows the need for insurers to draft exclusions crafted with offensive cyber operations in mind. The Exclusion Clauses released by the LMA in November 2021 do exactly this.
In the future, insurers will play a greater role in the narrative around offensive cyber operations. For example, the LMA’s choice of wording puts heavy emphasis on whether a government has attributed a cyber attack to a foreign state or its operatives. Notably, this does not include attributions made by cybersecurity vendors—an implicit value judgment. Although at present these decisions are just contractual language, insurance disputes are often argued in a court of law by opposing lawyers with million-dollar budgets. As such, scholars interested in offensive cyber operations should pay attention to the insurance industry, an actor beyond the “usual suspects”.
This blog post draws heavily on the article: Woods, D.W., Weinkle, J. Insurance definitions of cyber war. Geneva Pap Risk Insur Issues Pract 45, 639–656 (2020). https://doi.org/10.1057/s41288-020-00168-5.
Daniel W Woods is a Lecturer in Cybersecurity at the University of Edinburgh focusing on cyber risk measurement and management.

Leave a comment