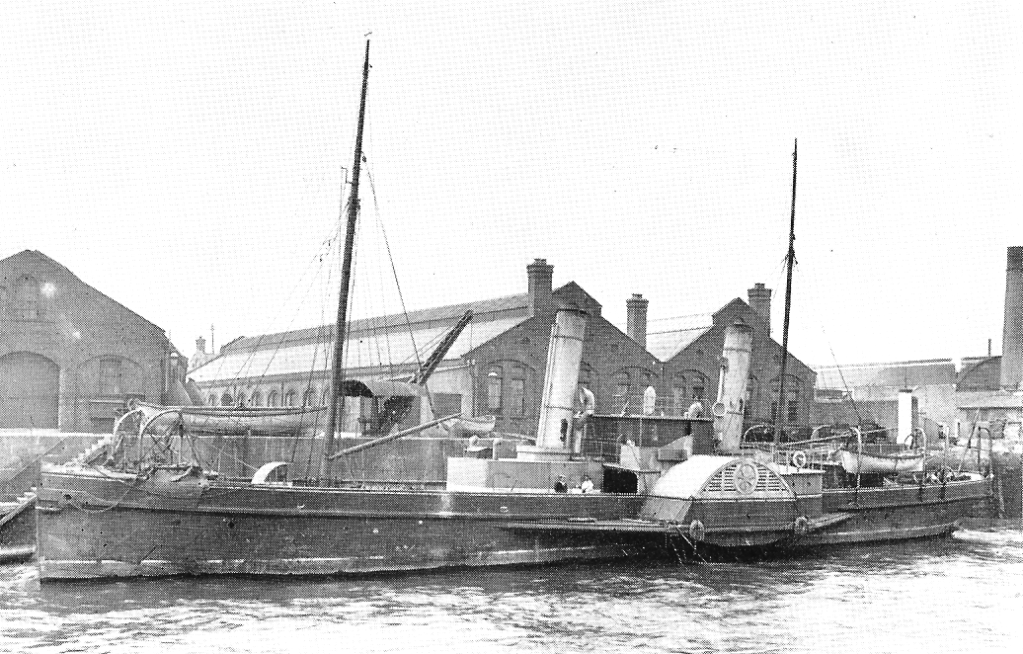
Image: An undated photograph of CS Alert. Source: Wikipedia.
By Neil Ashdown
On 5 August 1914 – the day after Great Britain declared war on Germany – CS Alert, a British cable ship, severed the submarine telegraph cables connecting Germany to the United States. The first post on The Alert, the blog of the Offensive Cyber Working Group (OCWG), asked whether this action was an early example of offensive cyber. In this post, I will argue that this historical case can help inform our understanding of offensive cyber operations today, more than a century later.
The relationship between secrecy and offensive cyber
CS Alert’s mission depended on tactical surprise – keeping the timing and nature of the ship’s departure secret increased its likelihood of success.[1] However, the severing of the cables would not have come as a strategic surprise to Germany or other world powers; a Peruvian vessel severed a submarine cable during the 1879-84 War of the Pacific and the US cut cables – including a British-owned cable – during the 1898 Spanish-American War.[2] Germany and other states had actively been promoting the use of wireless telegraphy (radio) precisely because it offered an alternative to dependence on British-owned cables.
This dynamic is relevant to the current secrecy around offensive cyber. Today, states are extremely reticent to provide any details about their offensive cyber capabilities. Some of this is about the preservation of capabilities that would be rendered ineffective by exposure, much as the details of Alert’s mission had to be kept secret. However, there is considerable over-classification,[3] likely stemming from the historical origin of state cyber capabilities within the instinctively secretive intelligence community.[4] In addition, as Ciaran Martin, former head of the UK National Cyber Security Centre, recently argued, such secrecy also allows policymakers an ‘easy option’ for threatening reprisals against hostile state activity, without having to go into details.[5]
Even though Alert’s mission depended on secrecy for its effectiveness, the goal of that mission and its impact were largely predictable based on information available in open sources at the time. At the risk of being proved dramatically wrong by some future revelation(s), something similar could be said about modern state cyber capabilities. Advanced cyber powers may have capabilities that could prompt surprise and outcry if revealed, but cyber capabilities are not ‘magical’. Indeed, like real-world magic tricks, once the secret is revealed, many cyber operations are less sophisticated than we tend to think.[6]
This does not mean that there will be no surprises for observers of offensive cyber. Similarly, public understanding of Britain’s campaign against Germany’s communications evolved over time. While it was immediately clear that the cables had been severed, the details of the operation were initially secret, leading to some incorrect claims. Fulwider notes that “[i]n much of the existing literature, the ship responsible for cutting the cable was reported as the Telconia.”[7] This underlines that public understanding of offensive cyber operations will need to be corrected in the future as more information becomes declassified.
Campaigns and context in offensive cyber
Alert’s mission was also part of a wider campaign to disrupt Germany’s communications. According to Winkler, “Historians have been aware of the severing of Germany’s cables in the Channel, but the larger scope of these operations has been obscured, as has the fact that Britain’s activities continued through to the final months of the war.”[8] Modern observers of offensive cyber would recognise this as a coherent campaign comprising many operations aimed at achieving strategic advantage.[9]
This campaign was not limited to technical measures. Winkler describes activities that would today fall under the rubric of human intelligence or covert action. These included a British intelligence agent sabotaging a German radio station in Mexico City, conducting counter-proliferation operations targeting key components[10], and using disinformation to eliminate the competition.[11] Similarly, far from being limited to computer network operations, it is likely that modern offensive cyber capabilities will often involve a combination of different approaches. Among other examples, this can be seen in public disclosures about Russian close access operations[12] and in the participation of the UK Secret Intelligence Service (MI6) in the UK’s National Cyber Force.[13]
The context of Alert’s mission is also important. The severing of the cables occurred at a time when the UK and Germany were in a state of armed conflict, London’s ultimatum to Germany having expired at 2300 on 4 August. In contrast, public understanding of what offensive cyber means, and what it is capable of, arises from a partial view of a subset of activities conducted outside of a state of armed conflict. Attempts to read across from ‘peacetime’ activities to the activities that states might conduct during a time of war need to bear this context in mind.[14]
Offensive cyber is an enabler of other activities, but it can also have unintended or undesirable consequences
Alert’s mission involved physically breaking equipment, but this was not its primary goal. Moreover, the operation was not intended to sever Germany’s communications with the outside world. Rather it was intended to force Berlin to use a more vulnerable channel – radio.[15] Highlighting the continuity between this operation and modern cyber operations, the Tallinn Manual 2.0[16] would describe this as ‘herding’.[17]
The campaign against German communications proved to be a force multiplier for other parts of the British war effort – monitoring of radio traffic increased the effectiveness of British efforts to interdict shipping intended for Germany. As Winkler observes, “[t]he resulting information blockade […] enabled Great Britain to reinforce the maritime blockade.”[18] The severing of the cable was also key component of a broader (dis)information operation conducted by Great Britain to shape perceptions among the US public and policymakers, peaking with the release of the disclosure of the Zimmerman telegram in 1917. The potential for such operations was recognised in the US immediately after Alert’s operation; according to Fulwider, “The New York Times reported the incident on 6 August, accurately pointing out that without direct cable connections, any word of events in Germany would have to pass through hostile channels.”[19]
Similarly, it is likely that modern offensive cyber operations will achieve effect not just through disrupting adversary systems (for example, wiping data or rendering devices inoperable), but through second-order effects. Herding and enabling information operations are two examples, as are large-scale degradation efforts targeting adversary counterintelligence capabilities.[20]
Not all the effects of offensive cyber operations will be intended or desirable. Winkler argues that “[t]he voyage of the Alert and its implications caused officials in the United States eventually to realize the strategic necessity of having an independent cable and radio network linking the nation to its overseas interests.”[21] US activities to reduce this vulnerability eroded the UK’s advantages in this area. Similarly, offensive cyber operations have the potential to draw an adversary’s attention to their vulnerabilities and spur them to develop capabilities of their own to respond.[22]
Efforts to promote norms around offensive cyber are not new
In a wider discussion of its policy on submarine telegraph cables, Kennedy notes that Britain initially attempted to promote international norms against cutting cables.[23] He cites an 1886 paper from the British government’s Colonial Defence Committee (CDC), recording “their strong opinion that no opportunity should be lost in defining the position of cables of neutrals, and in taking any steps likely to lead to the eventual neutralization of all cables by promoting an international sentiment in favour of them … […] Any degree of immunity, however small, which could be secured by Treaty, or by international sentiment, would therefore be a definite gain to the Empire.”
This claim resonates with concerns about the greater vulnerability of advanced digital economies in the event of cyber conflict. In language that almost exactly parallels modern statements about the United States’ vulnerability in this area, Kennedy notes that the CDC’s concern was driven by the recognition that “unrestricted cable-cutting would be on balance ‘a severe loss to the Empire, which would suffer mostly from this type of attack’”.[24] It is hardly surprising that states promote norms that are in their interests, as much around offensive cyber as around the ‘neutralization’ of submarine cables.[25] In the latter case, Britain’s effort to promote such norms quickly stalled, not least because “it was soon realized that it would be impossible to persuade other powers, particularly France and Russia, to accede to an international neutralization agreement.”[26]
As a result, Kennedy notes that Great Britain expanded and hardened its telegraph network.[27] This included the use of physical defences as well as deception to protect submarine cables.[28] This latter activity prefigures the use of deception for defence in cybersecurity.[29] Over time, the increased resilience of the network led to a shift in attitudes, and Great Britain downplayed efforts to promote norms around the neutralization of cables. By the time of the First World War, 28 years after the paper calling for neutralization, the British government had longstanding plans for disrupting the communications of potential adversaries. Efforts to promote norms gave way to an emphasis on resilience and offensive action by Britain to seize the initiative – paralleling in some respects the current debate over the US doctrine of persistent engagement.[30]
Offensive cyber is an outgrowth of other capabilities and resources
As Kennedy notes, this change in attitude reflected Britain’s awareness by 1911 that it “had so many advantages in this field that her own weaknesses were outweighed.” Britain controlled 60% of the world’s cables and key nodes in the global telegraph network were located on its territory. Moreover, Britain “possessed a virtual monopoly of the vital gutta-percha, which was used to insulate the wires [in undersea cables].”[31] It also had other – less tangible – advantages; its ownership of most of the world’s cables meant that Britain “knew more than anyone else about cable-laying or cable-cutting”.
There are parallels between Kennedy’s assessment of Britain’s power over telegraph cables in the 1900s and modern assessments of state cyber power. In general, states with more advanced technology sectors are more likely to have advanced cyber capabilities. As the International Institute of Strategic Studies (IISS) argued in its 2021 net assessment of state cyber capabilities, “strength in the core industries that underpin the future development of cyberspace is the decisive category [in determining a state’s cyber capability]”.[32] Similarly, the concentration of communication nodes on a state’s territory provides as much of an advantage today as it did with submarine telegraph cables, as does control over key resources – gutta-percha can be seen as the semiconductor chip of its day.[33]
The less tangible aspects remain important. Much as Britain’s know-how about cable laying contributed to its dominant position in this area, technical expertise also plays a role in cyber power. The IISS report describes “core cyber-intelligence capability” as lying “[a]t the heart of any nation’s cyber capability.”[34] Some of this capability will derive from technology and geographical position, as noted above, but perhaps even more decisive are the skills and expertise that a state’s intelligence apparatus can bring to bear.
Conclusion
CS Alert has been described as a central motif for the information society: “This one cableship represents strategies, technologies, ideas, and actions that still ripple though today’s technological, political, economic, and media landscape.”[35] The idea that Alert’s mission was an example of information warfare is uncontroversial. Gordon Corera describes it as “one of the first strategic acts of information warfare in the modern world […] leading to the birth of modern communications intelligence”.[36] Winkler asserts that “Information warfare in the electrical age is not a new phenomenon but dates from the late nineteenth century.”[37]
More debateable is whether it is analytically useful to view this operation as an early example of offensive cyber. As several members of the OCWG noted in a recent report, “The ‘prehistory’ of UK offensive cyber operations remains untold, although inevitably pre-dates their avowal by the UK in September 2013, the first country to do so.”[38] Is it helpful to extend this prehistory as far back as 1914, and indeed further? Or does grouping together a modern offensive cyber operation and Alert’s mission obscure the fundamental difference between a telegraph network, however highly developed, and networks of computational devices? If there really is a fundamental difference between 20th century signals intelligence and information warfare, on the one hand, and offensive cyber on the other, then examination of historical cases would be a way to identify this difference. In doing so, it could provide empirical evidence to advance theoretical debates about the nature of cyber conflict and intelligence.[39]
Moreover, highlighting elements of continuity between modern operations and historical operations that are now in the public record – such as Alert’s mission – could provide governments with a framework to talk more about offensive cyber, without revealing operational specifics. As IISS noted in its report, “On offensive cyber, it has so far proved difficult even to find the language for a more informed national and international public debate, but such an effort remains essential if the risks are to be properly managed.”[40] Exploring the similarities and differences between historical examples and modern offensive cyber would help support the development of that language. ‘Cyber’ can sometimes feel very abstract. Providing examples – such as Alert’s cable cutting early in the morning of 5 August 1914 – makes it more tangible.
Neil Ashdown is a PhD researcher in the Centre for Doctoral Training in Cyber Security for the Everyday at Royal Holloway University of London. He was formerly the deputy editor of Jane’s Intelligence Review.
[1] Gordon Corera, ‘How Britain Pioneered Cable-Cutting in World War One’, BBC News, 15 December 2017, sec. Europe, https://www.bbc.com/news/world-europe-42367551.
[2] Jonathan Reed Winkler, ‘Information Warfare in World War I’, The Journal of Military History 73, no. 3 (2009): 845–67, https://doi.org/10.1353/jmh.0.0324.
[3] Jason Healey and Robert Jervis, ‘Overclassification and Its Impact on Cyber Conflict and Democracy’, Modern War Institute, 22 March 2021, https://mwi.usma.edu/overclassification-and-its-impact-on-cyber-conflict-and-democracy/.
[4] Michael Warner, ‘Intelligence in Cyber—and Cyber in Intelligence – Understanding Cyber Conflict: 14 Analogies’, Carnegie Endowment for International Peace, 2017, https://carnegieendowment.org/2017/10/16/intelligence-in-cyber-and-cyber-in-intelligence-pub-73393.
[5] Ciaran Martin, ‘Ciaran Martin on Twitter: “It Is Pure Cyberbabble. The Gov’t Is in a Horrible Position Following Completely Unacceptable Iranian Behaviour. But Briefing Nonsense like This Doesn’t Help Anyone. Saying ‘Secret Cyber Strike’ Is Not a Policy Response & Shouldn’t Be a Pretext for Avoiding Hard Decisions 2/2” / Twitter’, accessed 3 August 2021, https://twitter.com/ciaranmartinoxf/status/1422435444470468608.
[6] Ben Buchanan, The Legend of Sophistication in Cyber Operations (Harvard Kennedy School, Belfer Center for Science and International Affairs, 2017).
[7] Chad R Fulwider, German Propaganda and US Neutrality in World War I (University of Missouri Press, 2017).
[8] Winkler, ‘Information Warfare in World War I’.
[9] Richard J. Harknett and Max Smeets, ‘Cyber Campaigns and Strategic Outcomes’, Journal of Strategic Studies 0, no. 0 (4 March 2020): 1–34, https://doi.org/10.1080/01402390.2020.1732354.
[10] Winkler, ‘Information Warfare in World War I’. “Mason then systematically acquired all of the eleven spare vacuum tubes in Mexico.”
[11] Winkler. “Mason would also go on to eliminate a German team headed to the coast with a smaller radio set by spreading the word that they carried diamonds (actually the crystal detectors used for receiving the signals). The team members were never heard from again.”
[12] Mark Odell, ‘How Dutch Security Service Caught Alleged Russian Spies | Financial Times’, Financial Times, 4 October 2018, https://www.ft.com/content/b1fb5240-c7db-11e8-ba8f-ee390057b8c9.
[13] ‘National Cyber Force Transforms Country’s Cyber Capabilities to Protect the UK’, accessed 12 May 2021, https://www.gchq.gov.uk/news/national-cyber-force.
[14] ‘Ciaran Martin: “Cyber Weapons Are Called Viruses for a Reason: Statecraft, Security and Safety in the Digital Age.”’, The Strand Group, accessed 23 July 2021, https://thestrandgroup.kcl.ac.uk/event/ciaran-martin-cyber-weapons-are-called-viruses-for-a-reason-statecraft-security-and-safety-in-the-digital-age/.
[15] Gordon Corera, Intercept: The Secret History of Computers and Spies (Hachette UK, 2015).
[16] Michael N Schmitt, Tallinn Manual 2.0 on the International Law Applicable to Cyber Operations (Cambridge University Press, 2017).
[17] Tallinn Manual 2.0, Rule 32, Comment 12: “As an example, a tactic of signals intelligence is to force adversaries to use forms of communication that are less secure so information can be collected. This driving, or ‘herding’, of enemy communications from a platform not susceptible to exploitation to a less secure one from which intelligence can be collected might be accomplished by physical damage to the former.”
[18] Winkler, ‘Information Warfare in World War I’.
[19] Fulwider, German Propaganda and US Neutrality in World War I.
[20] Horkos, ‘A Last Clever Knot?’, Medium, 24 November 2020, https://horkos.medium.com/a-last-clever-knot-26fd26765e8d.
[21] Jonathan Reed Winkler, Nexus (Harvard University Press, 2009).
[22] Andrea Shalal-Esa, ‘Iran Strengthened Cyber Capabilities after Stuxnet: U.S. General’, Reuters, 18 January 2013, sec. Technology News, https://www.reuters.com/article/us-iran-usa-cyber-idUSBRE90G1C420130118.
[23] P. M. Kennedy, ‘Imperial Cable Communications and Strategy, 1870-1914’, The English Historical Review 86, no. 341 (1971): 728–52.
[24] Kennedy.
[25] Perri Adams et al., ‘Responsible Cyber Offense – Lawfare’, accessed 3 August 2021, https://www.lawfareblog.com/responsible-cyber-offense.
[26] Kennedy, ‘Imperial Cable Communications and Strategy, 1870-1914’.
[27] Kennedy.
[28] Kennedy. “Another cunning measure at Esquimault was the laying of numerous dummy cables for a few miles out to sea to baffle an attempt at in-shore cutting.”
[29] See, for example, the work of the UK National Cyber Deception Laboratory (NCDL), as described in Neil Ashdown, ‘Mind Games: Deception Offers Role in Cyber Defence’, Jane’s Intelligence Review, 7 May 2020.
[30] Richard J Harknett, ‘SolarWinds: The Need for Persistent Engagement’, Lawfare, 23 December 2020, https://www.lawfareblog.com/solarwinds-need-persistent-engagement.
[31] Kennedy, ‘Imperial Cable Communications and Strategy, 1870-1914’.
[32] ‘Cyber Capabilities and National Power: A Net Assessment’, IISS, accessed 5 July 2021, https://www.iiss.org/blogs/research-paper/2021/06/cyber-capabilities-national-power.
[33] Kathrin Hille, ‘TSMC: How a Taiwanese Chipmaker Became a Linchpin of the Global Economy’, Financial Times, 24 March 2021, https://www.ft.com/content/05206915-fd73-4a3a-92a5-6760ce965bd9.
[34] ‘Cyber Capabilities and National Power’.
[35] R David Lankes, Forged in War: How a Century of War Created Today’s Information Society (Rowman & Littlefield Publishers, 2021).
[36] Corera, Intercept: The Secret History of Computers and Spies.
[37] Winkler, ‘Information Warfare in World War I’.
[38] Joe Devanny et al., ‘The National Cyber Force That Britain Needs?’, 2021.
[39] Robert Chesney and Max Smeets, ‘Policy Roundtable: Cyber Conflict as an Intelligence Contest’, Texas National Security Review, 17 September 2020, http://tnsr.org/roundtable/policy-roundtable-cyber-conflict-as-an-intelligence-contest/.
[40] ‘Cyber Capabilities and National Power’.

Leave a comment